Recommended Apps and Services
all recommended tools are free and open source unless otherwise noted.
-
Delete Me - a paid service to scrub your personal information from search engines and data brokers.
Delete Me's business is to do the annoying work for you, to get your information off of data broker sites. You can do this work yourself, as described in the following guides:
-
End-to-End Encrypted Messaging & Calling
-
Signal - like regular texting, group chatting, and calling, but with privacy built in - best choice for most users
-
Jitsi - video conferencing platform, similar to Zoom. paid service upgrades available.
-
Matrix - like Discord, Slack, Mattermost, or IRC
-
Briar and
Cwtch - like Signal, but peer-to-peer only. recommended for advanced users.
-
End-to-End Encrypted Email
-
1Password - paid closed-source password management service.
-
though 1Password is closed-source, I'm willing to forgive that for a few reasons:
-
1Password uses, ironically, a 2-key cryptographic system to encrypt your password vault (don't worry, you only have to remember one day-to-day).
- they publish the results of regular 3rd-party audits and certifications (this is industry-standard practice, but I like what I see of how they do it anyways)
-
they've published a whitepaper explaining the design of 1Password in nerdy detail
-
if you'd still prefer an open-source password management option, try Bitwarden, Proton Pass, or a flavor of KeePass - check the Privacy Guides page about password managers for a more detailed discussion
-
password managers are a hotly debated topic in privacy nerd circles, for plenty of valid reasons. some folks (like this former Google Project Zero researcher) will tell you to use your browser's password manager, while others will balk at anything except a self-hosted password vault. I am recommending services that I think are the best combination of usable by the average person, and well-designed and executed for privacy and security.
-
Malwarebytes - antivirus software for most phones and computers. not open source. paid service upgrades available.
-
TailsOS - portable anonymizing operating system
-
Filesharing
-
CryptPad - encrypted filesharing service. good alternative to Google Drive for collaborative file editing. paid service upgrades available. excellent security options with per-file granularity available.
-
Riseup Pad - ephemeral encrypted filesharing service
-
Proton Drive - Google Drive replacement
-
Web Browsers
-
VPNs
basic things to look for when choosing a VPN: a no-logs policy confirmed by independent audit, a warrant canary, parent company based in a country where privacy laws favor the consumer, parent company not owned by an advertising or data broker entity
-
Surfshark
-
Mullvad
is my foremost VPN recommendation for the privacy-conscious, for a few reasons:
-
neither names, addresses, phone numbers, nor email addresses are required to get a Mullvad VPN subscription. accounts are tied to random 16-digit numbers
-
you can pay for your subscription with cash, Monero, bank wire-transfer, credit card, Bitcoin, Bitcoin Cash, PayPal, Swish, EPS Transfer, Bancontact, iDEAL, Przelewy24, and vouchers sold by resellers. this variety of options tells me that Mullvad understands that privacy isn't something you can achieve with one tool or strategy alone.
-
Mullvad's feature selection is up-to-date with current industry knowledge on privacy-invading practices; for example, they offer DAITA: Defense Against AI-guided Traffic Analysis to combat statistical categorization of your internet activity based on metadata
-
Swedish authorities have tried executing a warrant for customer data on Mullvad's offices in 2023, and had to walk away empty-handed
-
as a policy, Mullvad doesn't do influencer sponsorships
-
Proton VPN
Further Guides to Recommended Apps
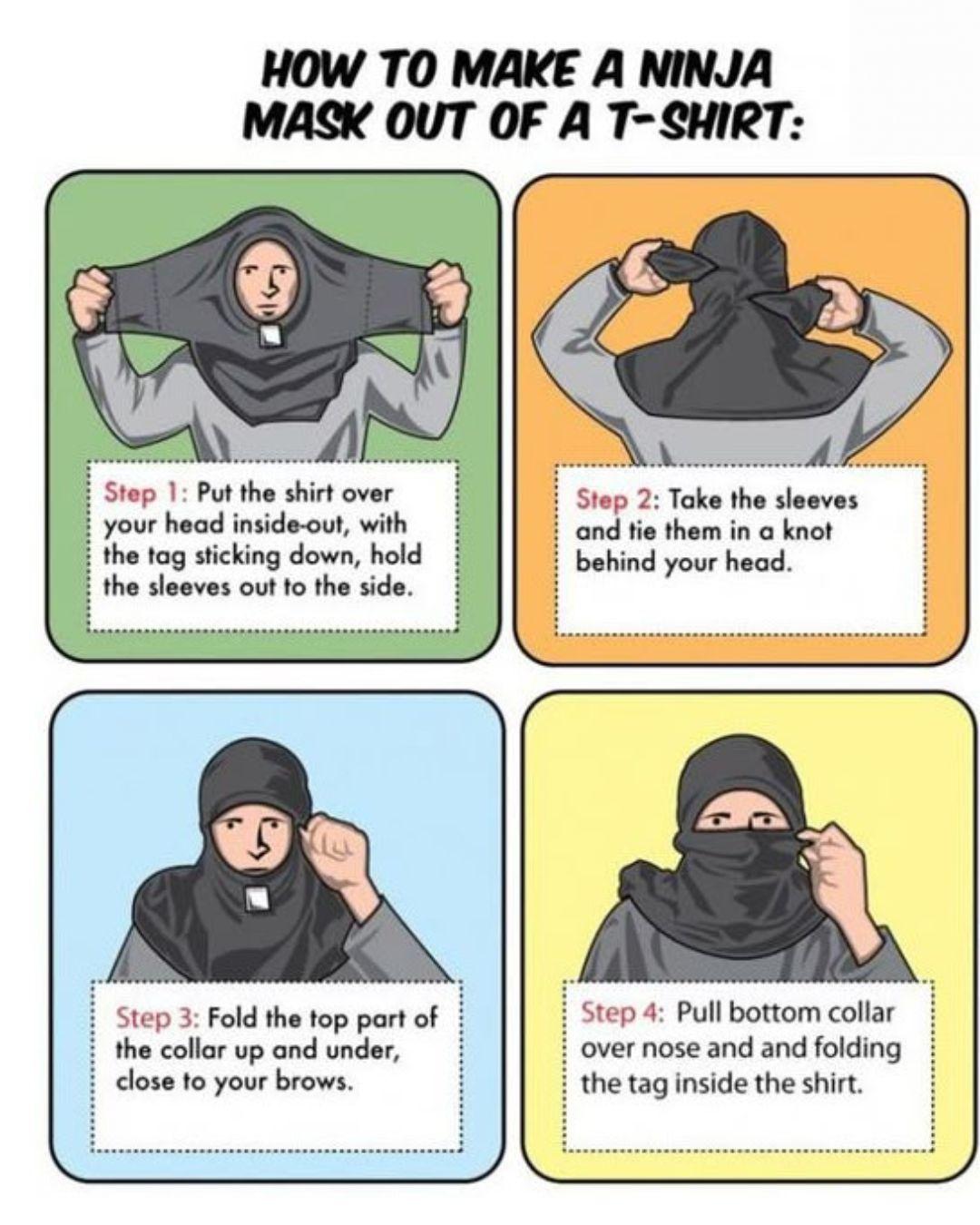
![((The comic illustrates the relative strength of passwords assuming basic knowledge of the system used to generate them. A set of boxes is used to indicate how many bits of entropy a section of the password provides. The comic is laid out with 6 panels arranged in a 3x2 grid. On each row, the first panel explains the breakdown of a password, the second panel shows how long it would take for a computer to guess, and the third panel provides an example scene showing someone trying to remember the password.))
[[The password ''Tr0ub4dor&3'' is shown in the centre of the panel. A line from each annotation indicates the word section the comment applies to.]]
Uncommon (non-gibberish) base word [[Highlighting the base word - 16 bits of entropy.]]
Caps? [[Highlighting the first letter - 1 bit of entropy.]]
Common Substitutions [[Highlighting the letters 'a' (substituted by '4') and both 'o's (the first of which is substituted by '0') - 3 bits of entropy.]]
Punctuation [[Highlighting the symbol appended to the word - 4 bits of entropy.]]
Numeral [[Highlighting the number appended to the word - 3 bits of entropy.]]
Order unknown [[Highlighting the appended characters - 1 bit of entropy.]]
(You can add a few more bits to account for the fact that this is only one of a few common formats.)
~28 bits of entropy
2^28 = 3 days at 1000 guesses
sec
(Plausible attack on a weak remote web service. Yes, cracking a stolen hash is faster, but it's not what the average user should worry about.)
Difficulty to guess: Easy.
[[A person stands scratching their head trying to remember the password.]]
Person: Was it trombone? No, Troubador. And one of the Os was a zero?
Person: And there was some symbol...
Difficulty to remember: Hard.
[[The passphrase ''correct horse battery staple'' is shown in the centre of the panel.]]
Four random common words {{Each word has 11 bits of entropy.}}
~44 bits of entropy.
2^44 = 550 years at 1000 guesses
sec
Difficulty to guess: Hard.
[[A person is thinking, in their thought bubble a horse is standing to one side talking to an off-screen observer. An arrow points to a staple attached to the side of a battery.]]
Horse: That's a battery staple.
Observer: Correct!
Difficulty to remember: You've already memorized it
((The caption below the comic reads: Through 20 years of effort, we've successfully trained everyone to use passwords that are hard for humans to remember, but easy for computers to guess.))
{{Title text: To anyone who understands information theory and security and is in an infuriating argument with someone who does not (possibly involving mixed case), I sincerely apologize.}}](https://imgs.xkcd.com/comics/password_strength.png)